The Architecture of Inviolable Digital Custody.
Enterprise virtual asset security is no longer about perimeter defense. It is about engineering absolute physical and logic-based resilience into the very fabric of your corporate workflow.
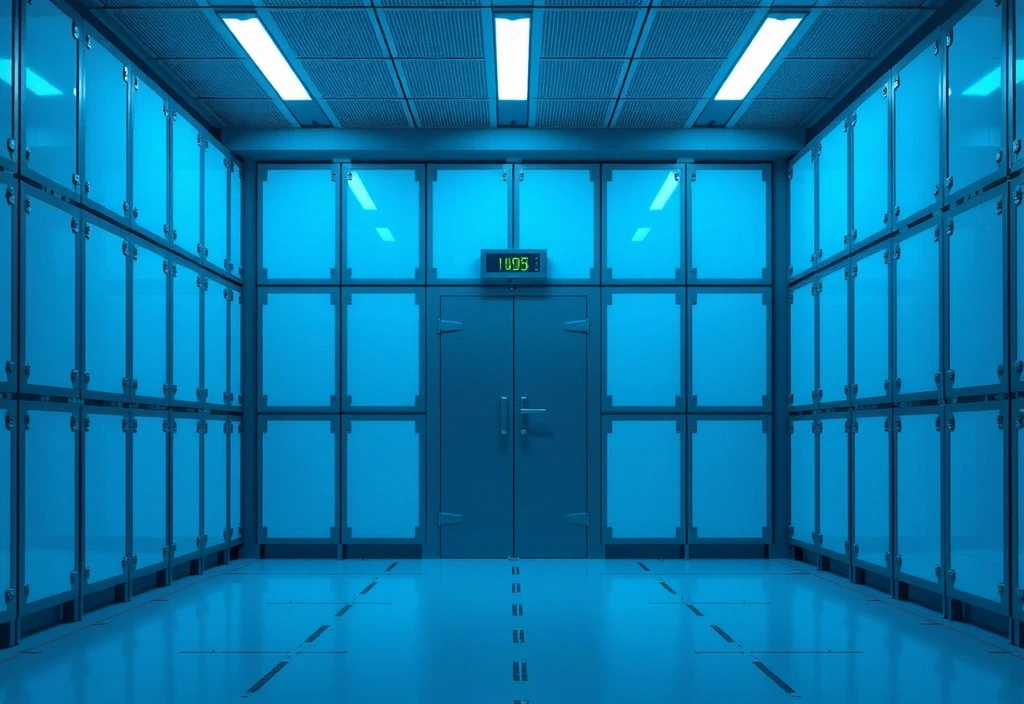
Physical Integrity via Multi-Layer Hardware Security
We move beyond standard storage solutions. Our approach prioritizes air-gapped environments and specialized hardware security modules (HSM) that ensure no single point of failure can compromise your corporate holdings.
-
Hardware Security Modules (HSM)
Dedicated physical processors designed to safeguard the digital life cycle of your keys.
-
Biometric Access Isolation
Multi-factor physical authentication protocols integrated directly into hardware interaction.
-
Faraday Cage Storage
Shielding devices from electromagnetic interference and remote signal exploits.

The Multi-Sig Governance Matrix
Corporate digital security is as much about human hierarchy as it is about cryptography. We implement Multi-Signature (Multi-Sig) frameworks that distribute authority and eliminate rogue behavior risks.
M-of-N Authorization
Transaction execution requires approval from a predetermined subset of key holders. This ensures that even if one internal signatory is compromised, the assets remain shielded behind a wall of collective consensus.
Threshold Cryptography
By splitting private keys into sensitive fragments distributed across multiple secure locations in Mumbai and global vaults, we ensure the full key never exists in one place at any single time.
Time-Locked Protocol
Critical asset movements can be subject to mandatory dwell times, allowing security teams to verify and intervene if an unauthorized attempt is detected within the cooldown window.

The Failure Cycle
Most enterprises fail not because of external hackers, but because of poor key hygiene and centralized power. Our framework forces institutional discipline through automated governance.
Explore Compliance OptionsField Guide to Resilience
A structured approach to transitioning from software-based vulnerability to operational hardening.
Phase: Asset Discovery & Risk Mapping
Before securing, one must catalog. We map every digital touchpoint within your organization, identifying "hidden" hotspots where assets may reside outside of official governance. This map forms the foundation of your tailored security perimeter.

Phase: Hardware Transitioning
Assets are migrated from vulnerable desktop environments to cold-storage hardware protocols. This migration is performed within controlled air-gapped zones in accordance with ISO-level security standards, ensuring keys are never exposed to the networked world.

Phase: Recursive Auditing
Security is a state of perpetual maintenance. Our framework includes scheduled recursive audits of both the hardware integrity and the credential status of all signatories, ensuring the human element remains as robust as the technological one.

Requirement Logic: Identifying Your Custody Level
Standard Enterprise
Suited for organizations holding static assets for long-term periods with minimal quarterly movements.
High-Velocity Institutional
Designed for active treasury management requiring weekly movements with high-stakes authorization.
Ready to Fortress Your Assets?
Secure your corporate future today with the help of Mumbai’s leading digital asset security architects. We don't just bridge gaps; we close them permanently.